Why your company needs a phishing programme
A phishing programme in your organisation allows you to test the likely response you would see from your colleagues, should they receive a malicious phishing email. How many of your colleagues are vulnerable?
It only takes one person to click for your organisation to be compromised and your expensive security controls to unravel.
Did you know that phishing is the primary delivery vector for ransomware?
Several high-profile companies have been infected by ransomware recently, causing their operations to seize. Travelex saw their websites taken down and their operations revert to pen and paper for a month due to crippling ransomware.
Training staff on how to spot and respond to a suspected phishing email can be one of the best security investments you make. The potential financial, reputational and regulatory consequences of not training staff can shut your business down. Read our article on balancing security risk and budget.
What is ransomware?
Ransomware is a malicious software or virus that holds the victim’s data or devices “hostage” until a fee is paid for its release. Many criminals will use ransomware to encrypt data files and will ask the victim to pay them a certain amount of bitcoin for the decryption key.

Phishing programmes do need time, attention and budget but the investment will help to reduce the risk of a successful cyber-attack. Not only that, they will provide you with these two key insights:
1. The level of phishing awareness within your organisation through the click rate.
2. The ease and awareness of your phishing reporting process.
Click Rate
The fundamental KPI that a phishing tool will give you is your click rate. How many people fell for the phish? Campaigns are unlikely to get a 0% click rate but it’s important to keep this number as low as possible. KnowBe4 have provided a benchmarking white paper which you can use to compare your results to others in your sector.
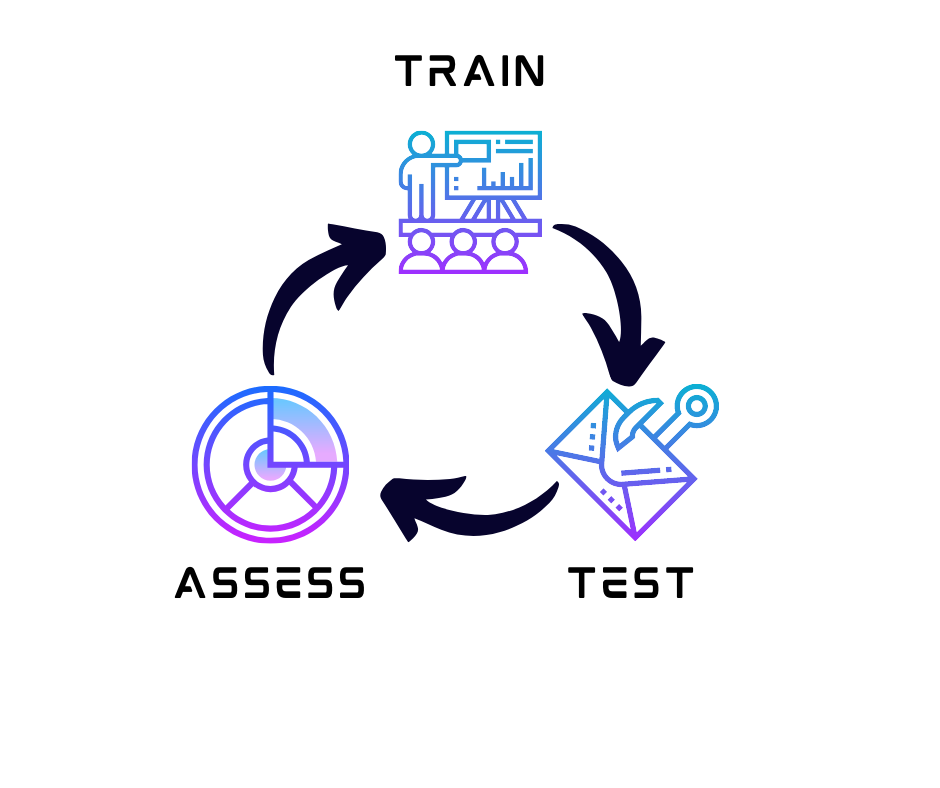
Ideally you want to see the click rate reduce each time you do a phishing exercise, but you must provide training before you look to reassess. This can be done through face-to-face training, eLearning modules, team cascades or intranet articles but it is important to be specific and teach staff the anatomy of phishing emails. Show them examples and the consequences of falling for these types of emails both in work and at home. Find out more about our security awareness kits.
What about staff who just keep clicking?
As you get into the rhythm of running regular phishing campaigns, you may find the same people are clicking and falling for the phish. In order to build a positive security culture, it is important not to punish people or make them feel humiliated for clicking. Staff must feel comfortable speaking to security when they make a mistake or contacting security to report potential incidents, the team must be approachable. We are all susceptible to being phished.
If staff keep clicking, you have to take a step back and look at the training you are providing. The phishing campaign is your measure of how well the training is understood so if it is boring and/or time consuming, chances are the messages are not landing.
Aside from training, talk to the communications team and make sure all company emails do not resemble a phishing email. Sometimes HR or finance emails can be auto-generated and look suspiciously like a phishing email or give users a deadline for when they must click the link or return the attachment. If these types of emails are common in your company, work with the communication team to find a better way of working.
Reporting Process
Do you believe the process for reporting phishing emails is easy and has been well communicated? There is no better way to try it out than through your phishing campaign. Ideally when you launch your campaign, your report phishing mailbox or service should be inundated, if its not then you know this needs to be addressed in your training plan.
What you may find instead, is that staff forward the email onto their teammates and ask their opinion. Or you may see some questions on your internal social channels or you find queries being sent to senior managers or leaders on whether the business is being targeted.
The first response should be for people to report the email and they should never forward it on to their colleagues. After it is reported, asking other colleagues if they received it or emailing the security team about it is ok, but its’ important to stress to colleagues, the quicker they report it, the quicker the security team can investigate.
Stick to the plan or pivot
Training is essential and goes hand in hand with a phishing programme. You cannot have one without the other.
It is important to assess your training plan after each phishing exercise, do your staff need awareness sessions on areas you had not anticipated or planned for? Are the previous training messages being understood? If your click rate is reducing and you are seeing more people follow the reporting process then you may want to stick to the plan, but if you aren’t seeing progress it’s important to re-evaluate and be willing to pivot. Try something different, a new approach to your training or a new style of communications.
Recap
You should now understand why it is vital to have a phishing programme and a bit more about the security awareness cycle. Time to get started?
We know it can be difficult to fund these programmes, get leadership buy in or have the time to dedicate to security awareness if you are a small team. That is why we have developed a resource kit full of expertly written and developed security awareness materials that you just need to push out to staff. We have made it as easy as possible to train your staff. If you want more information on our kits, help with leadership buy in, on-site awareness training or developing a strategy for your business, then get in touch with Neon Circle.




